[The] Intelligence National Security Alliance. INSA is a powerful but
little-known coalition established in 2005 by companies working for the National Security Agency. In recent years, it has become the premier organization for the men and women who run the massive cyberintelligence-industrial complex that encircles Washington, DC…[One such company is founded by] former Navy SEAL named Melchior Baltazar, the CEO of an up-and-coming company called SDL Government. Its niche, an eager young flack explained, is providing software that military agencies can use to translate hundreds of thousands of Twitter and Facebook postings into English and then search them rapidly for potential clues to terrorist plots or cybercrime.
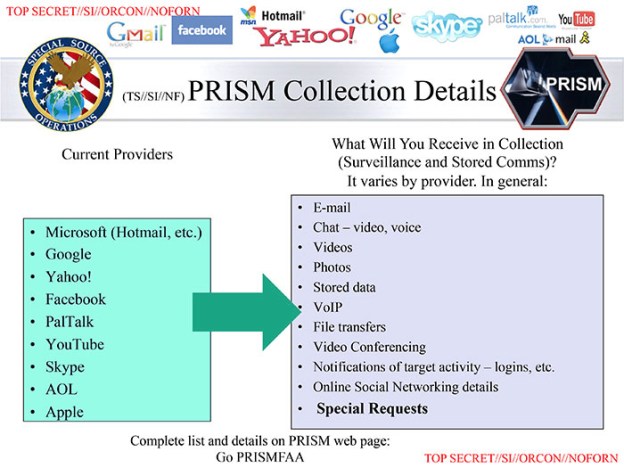
It sounded like the ideal tool for the NSA. Just a few months earlier, Snowden had leaked documents revealing a secret program called PRISM, which gave the NSA direct access to the servers of tech firms, including Facebook and Google. He had also revealed that the NSA and its British counterpart, the GCHQ, had special units focused on cracking encryption codes for social media globally….
This small company, and INSA itself, are vivid examples of the rise of a new class in America: the cyberintelligence ruling class. These are the people—often referred to as “intelligence professionals”—who do the actual analytical and targeting work of the NSA and other agencies in America’s secret government. Over the last 15 years, thousands of former high-ranking intelligence officials and operatives have left their government posts and taken up senior positions at military contractors, consultancies, law firms, and private-equity firms. In their new jobs, they replicate what they did in government—often for the same agencies they left. But this time, their mission is strictly for-profit.
Take Olsen, who served as general counsel for the NSA and as a top lawyer for the Justice Department before joining the National Counter-Terrorism Center (NCTC). He is now the president for consulting services of IronNet Cybersecurity, the company founded last year by Army Gen. Keith Alexander, the longest-
serving director in the history of the NSA. The firm is paid up to $1 million a month to consult with major banks and financial institutions in a “cyber war council” that will work with the NSA, the Treasury Department, and other agencies to deter cyberattacks that “could trigger financial panic,” Bloomberg reported last July 2014.
Some members of this unique class are household names. Most cable-news viewers, for example, are familiar with Michael Chertoff and Michael Hayden, two of the top national-security officials in the Bush administration. In 2009, they left their positions at the Justice Department and the NSA, respectively, and created the Chertoff Group, one of Washington’s largest consulting firms, with a major emphasis on security..
Well, enough, you might say: Isn’t this simply a continuation of Washington’s historic revolving door? The answer is no. As I see it, the cyberintelligence- industrial complex is qualitatively different from—and more dangerous than—the military-industrial complex identified by President Eisenhower in his famous farewell address. This is because its implications for democracy, inequality, and secrecy are far more insidious….To confront the surveillance state, we also have to confront the cyberintelligence ruling class and expose it for what it really is: a joint venture of government officials and private-sector opportunists with massive power and zero accountability.
Excerpts from Tim Shorrock, How Private Contractors Have Created a Shadow NSA, Nation, May 27, 2015.