The Starlink constellation of SpaceX currently consists of 3,335 active satellites and has become an integral part of Ukraine’s military and civil response to Russia’s invasion…Appropriately enough, the story started with a tweet, one sent by Mykhailo Fedorov, Ukraine’s minister of digital transformation, two days after the invasion:
@elonmusk, while you try to colonize Mars —Russia try to occupy Ukraine! While your rockets successfully land from space—Russian rockets attack Ukrainian civil people! We ask you to provide Ukraine with Starlink stations and to address sane Russians to stand.
Mr Musk replied to him within hours, saying that the Starlink service had been turned on over Ukraine and that the hardware would follow. Within days lorries full of the pizza-sized flat dishes used to access the satellites began to arrive in Ukraine.
By May 2022 around 150,000 people were using the system every day. The government quickly grew to rely on it for various communication needs, including, on occasion, the transmission of the nightly broadcast by Volodymyr Zelensky, Ukraine’s president. Because the dishes and their associated terminals are easily portable and can be rigged to run off a car battery, they are ideal for use in a country where the electricity and communication networks are regularly pounded by Russian missiles. When Kherson was liberated in November 2022 Starlink allowed phone and internet services to resume within days.
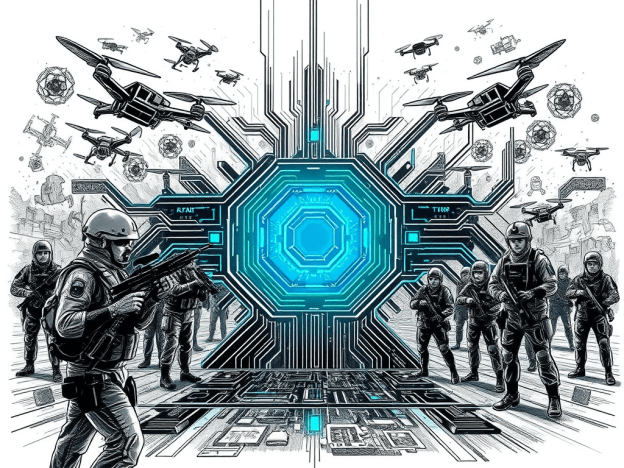
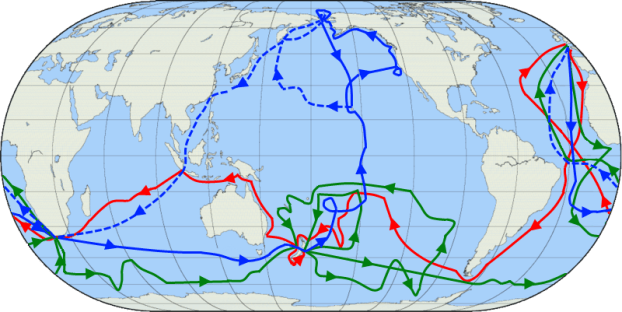
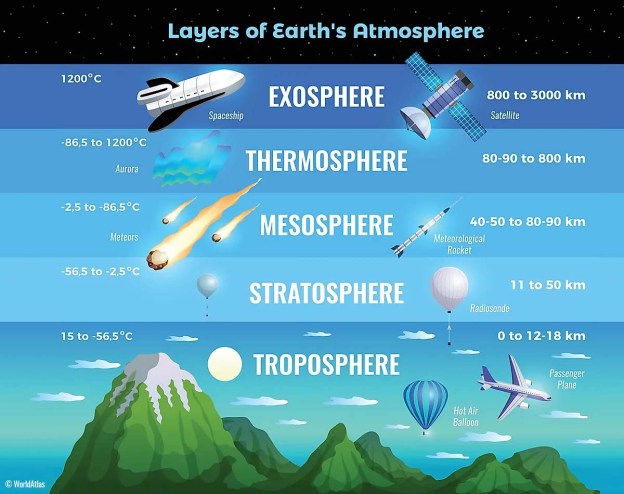
Crucially, Starlink has become the linchpin of what military types call C4ISR (command, control, communications, computers, intelligence, surveillance and reconnaissance). Armies have long relied on satellite links for such things…But Most satellite communications make use of big satellites which orbit up at 36,000km. Perched at such a height a satellite seems to sit still in the sky, and that vantage allows it to serve users spread across very large areas. But even if such a satellite is big, the amount of bandwidth it can allocate to each user is often quite limited.
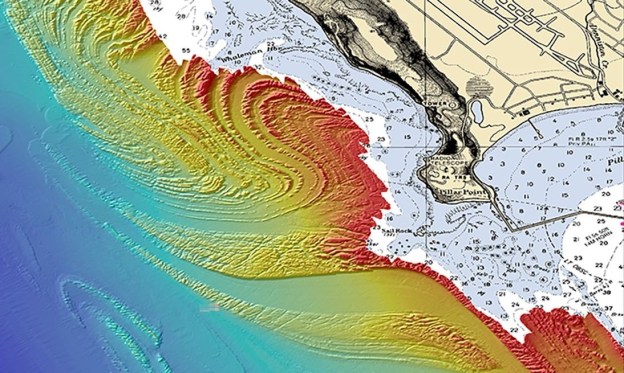
The orbits used by Starlink’s much smaller satellites are far lower: around 550km. This means that the time between a given satellite rising above the horizon and setting again is just minutes. To make sure coverage is continuous thus requires a great many satellites, which is a hassle. But because each satellite is serving only a small area the bandwidth per user can be high. And the system’s latency—the time taken for signals to get up to a satellite and back down to Earth—is much lower than for high-flying satellites.
Franz-Stefan Gady, of the International Institute for Strategic Studies, a think-tank, recently visited the Ukrainian front lines and saw an example of what cheap, ubiquitous connectivity makes possible: a sort of Uber for howitzers. .. “Ukrainian military operations are hugely dependent on having access to the internet,” says Mr Gady, “so Starlink is a most critical capability.” A Ukrainian soldier puts it more starkly. “Starlink is our oxygen,” he says. Were it to disappear “Our army would collapse into chaos.”…
Starlink signals are strong compared with those from higher flying satellites, which makes jamming them harder. And the way that the dishes use sophisticated electronics to create narrow, tightly focused beams that follow satellites through the sky like invisible searchlights provides further resistance to interference…
If its signals cannot be jammed, the system itself could be attacked instead….Cyber-attacks like the one aimed at Ukraine’s legacy satellite system on February 24, 2022 are one possibility. So far, though, similar sallies against Starlink appear to have been ineffective, in part thanks to SpaceX’s ability to quickly update the system’s software. Dave Tremper, director of electronic warfare for the Office of the Secretary of Defense, has said the speed of the software response he witnessed to one attack was “eye-watering”.
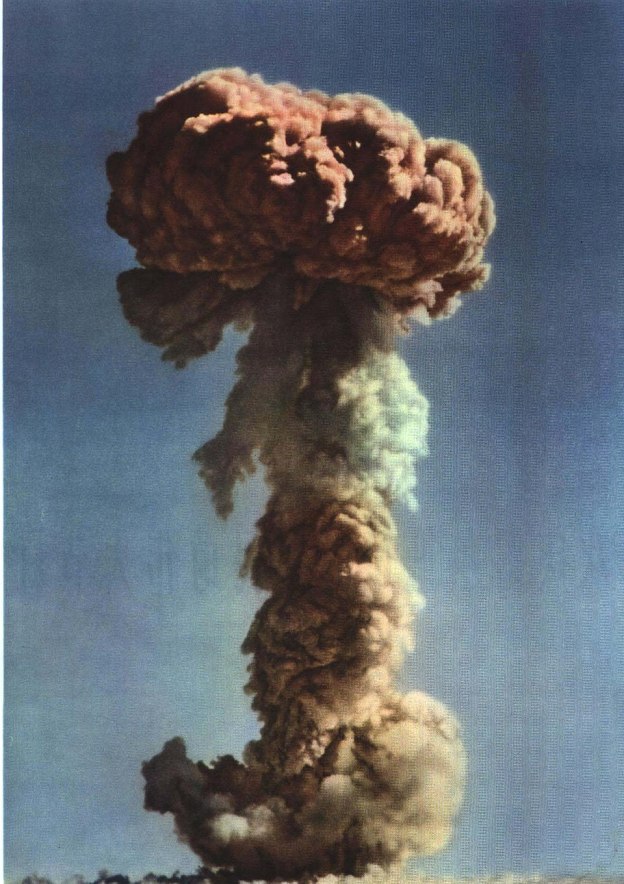
And then there are the satellites themselves. America, China, India and Russia have missiles that can shoot satellites out of the sky. Again, though, using them would seem a severe escalation. It would also be a lot less useful against a constellation like Starlink than against older systems. Knocking out a single Starlink would achieve more or less nothing. If you want to damage the space-based bit of the system, you need to get rid of lots of them…
In 2020 China filed documents with the International Telecommunication Union, a UN body, for a 13,000-satellite constellation of its own.
Excerpts from The Satellites that Saved Ukraine, Economist, Jan. 7, 2023