The federal government has significantly expanded undercover operations in recent years, with officers from at least 40 agencies posing as business people, welfare recipients, political protesters and even doctors or ministers to ferret out wrongdoing, records and interviews show. At the Supreme Court, small teams of undercover officers dress as students at large demonstrations outside the courthouse and join the protests to look for suspicious activity, according to officials familiar with the practice.
At the Internal Revenue Service, dozens of undercover agents chase suspected tax evaders worldwide, by posing as tax preparers, accountants drug dealers or yacht buyers and more, court records show. At the Agriculture Department, more than 100 undercover agents pose as food stamp recipients at thousands of neighborhood stores to spot suspicious vendors and fraud, officials said…But outside public view, changes in policies and tactics over the last decade have resulted in undercover teams run by agencies in virtually every corner of the federal government, according to officials, former agents and documents….
“Done right, undercover work can be a very effective law enforcement method, but it carries serious risks and should only be undertaken with proper training, supervision and oversight,” said Michael German, a former F.B.I. undercover agent who is a fellow at New York University’s law school. “Ultimately it is government deceitfulness and participation in criminal activity, which is only justifiable when it is used to resolve the most serious crimes.”…
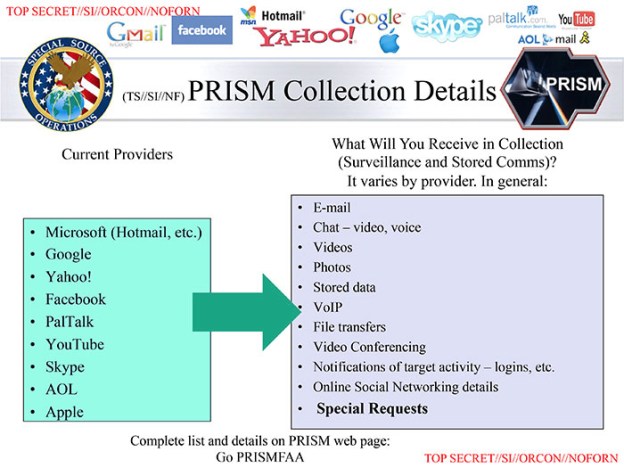
the Drug Enforcement Administration stoked controversy after disclosures that an undercover agent had created a fake Facebook page from the photos of a young woman in Watertown, N.Y. — without her knowledge — to lure drug suspects. And in what became a major political scandal for the Obama administration, agents from the Bureau of Alcohol, Tobacco, Firearms and Explosives allowed guns to slip into Mexico in 2011 in an operation known as Fast and Furious that involved undercover operations. In response to that episode, the Justice Department issued new guidelines to prosecutors: …Before prosecutors approve such tactics, the previously undisclosed guidelines require that they consider whether an operation identifies a “clearly defined” objective, whether it is truly necessary, whether it targets “significant criminal actors or entities,” and other factors, the officials said.
Those guidelines apply only to the law enforcement agencies overseen by the Justice Department. Within the Treasury Department, undercover agents at the I.R.S., for example, appear to have far more latitude than do those at many other agencies. I.R.S. rules say that, with prior approval, “an undercover employee or cooperating private individual may pose as an attorney, physician, clergyman or member of the news media.”…
Oversight, though, can be minimal…Detailed reviews of the money spent by IRS in some of its undercover operations took as long as four and a half years to complete, according to a 2012 review by the Treasury Department’s inspector general. Across the federal government, undercover work has become common enough that undercover agents sometimes find themselves investigating a supposed criminal who turns out to be someone from a different agency, law enforcement officials said. In a few situations, agents have even drawn their weapons on each other before realizing that both worked for the federal government…
It is impossible to tell how effective the government’s operations are or evaluate whether the benefits outweigh the costs, since little information about them is publicly disclosed. Most federal agencies declined to discuss the number of undercover agents they employed or the types of investigations they handled. The numbers are considered confidential and are not listed in public budget documents, and even Justice Department officials say they are uncertain how many agents work undercover….
At the Supreme Court, all of the court’s more than 150 police officers are trained in undercover tactics, according to a federal law enforcement official speaking on condition of anonymity because it involved internal security measures. At large protests over issues like abortion, small teams of undercover officers mill about — usually behind the crowd — to look for potential disturbances.The agents, often youthful looking, will typically “dress down” and wear backpacks to blend inconspicuously into the crowd, the official said…. The use of undercover officers is seen as a more effective way of monitoring large crowds.
A Supreme Court spokesman, citing a policy of not discussing security practices, declined to talk about the use of undercover officers. Mr. German, the former F.B.I. undercover agent, said he was troubled to learn that the Supreme Court routinely used undercover officers to pose as demonstrators and monitor large protests. “There is a danger to democracy,” he said, “in having police infiltrate protests when there isn’t a reasonable basis to suspect criminality
Excerpt from ERIC LICHTBLAU and WILLIAM M. ARKINNOV, More Federal Agencies Are Using Undercover Operations, NY Times, Nov 15, 2014