On 7 March 2017, WikiLeaks began its new series of leaks on the U.S. Central Intelligence Agency…code-named “Vault 7” by WikiLeaks..
On 7 March 2017, WikiLeaks began its new series of leaks on the U.S. Central Intelligence Agency…code-named “Vault 7” by WikiLeaks..
The first full part of the series, “Year Zero”, comprises 8,761 documents and files from an isolated, high-security network situated inside the CIA’s Center for Cyber Intelligence in Langley, Virgina. It follows an introductory disclosure last month of CIA targeting French political parties and candidates in the lead up to the 2012 presidential election.
“Year Zero” introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones….
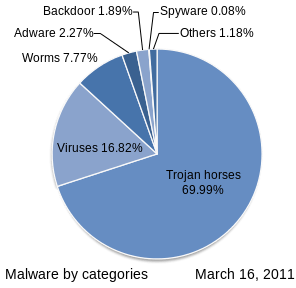
By the end of 2016, the CIA’s hacking division, which formally falls under the agency’s Center for Cyber Intelligence (CCI), had over 5000 registered users and had produced more than a thousand hacking systems, trojans, viruses, and other “weaponized” malware. Such is the scale of the CIA’s undertaking that by 2016, its hackers had utilized more code than that used to run Facebook. The CIA had created, in effect, its “own NSA”…
Once a single cyber ‘weapon’ is ‘loose’ it can spread around the world in seconds, to be used by rival states, cyber mafia and teenage hackers alike.
CIA malware and hacking tools are built by EDG (Engineering Development Group), a software development group within CCI (Center for Cyber Intelligence), a department belonging to the CIA’s DDI (Directorate for Digital Innovation)…. Malware called “Weeping Angel”, developed by the CIA’s Embedded Devices Branch (EDB), infests smart TVs, transforming them into covert microphones… The attack against Samsung smart TVs was developed in cooperation with the United Kingdom’s MI5/BTSS. After infestation, Weeping Angel places the target TV in a ‘Fake-Off’ mode, so that the owner falsely believes the TV is off when it is on. In ‘Fake-Off’ mode the TV operates as a bug, recording conversations in the room and sending them over the Internet to a covert CIA server.
As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks. The purpose of such control is not specified, but it would permit the CIA to engage in nearly undetectable assassinations.
The CIA’s Mobile Devices Branch (MDB) developed numerous attacks to remotely hack and control popular smart phones. Infected phones can be instructed to send the CIA the user’s geolocation, audio and text communications as well as covertly activate the phone’s camera and microphone.
Despite iPhone’s minority share (14.5%) of the global smart phone market in 2016, a specialized unit in the CIA’s Mobile Development Branch produces malware to infest, control and exfiltrate data from iPhones and other Apple products running iOS, such as iPads. CIA’s arsenal includes numerous local and remote “zero days” developed by CIA or obtained from GCHQ, NSA, FBI or purchased from cyber arms contractors such as Baitshop. The disproportionate focus on iOS may be explained by the popularity of the iPhone among social, political, diplomatic and business elites.
A similar unit targets Google’s Android which is used to run the majority of the world’s smart phones (~85%) including Samsung, HTC and Sony. 1.15 billion Android powered phones were sold last year. “Year Zero” shows that as of 2016 the CIA had 24 “weaponized” Android “zero days” which it has developed itself and obtained from GCHQ, NSA and cyber arms contractors.
These techniques permit the CIA to bypass the encryption of WhatsApp, Signal, Telegram, Wiebo, Confide and Cloackman by hacking the “smart” phones that they run on and collecting audio and message traffic before encryption is applied.
The CIA also runs a very substantial effort to infect and control Microsoft Windows users with its malware.
Attacks against Internet infrastructure and webservers are developed by the CIA’s Network Devices Branch (NDB). The CIA has developed automated multi-platform malware attack and control systems covering Windows, Mac OS X, Solaris, Linux and more, such as EDB’s “HIVE” and the related “Cutthroat” and “Swindle” tools, which are described in the examples section below.
Cyber ‘weapons’ are in fact just computer programs which can be pirated like any other. Since they are entirely comprised of information they can be copied quickly with no marginal cost. Securing such ‘weapons’ is particularly difficult since the same people who develop and use them have the skills to exfiltrate copies without leaving traces — sometimes by using the very same ‘weapons’ against the organizations that contain them. There are substantial price incentives for government hackers and consultants to obtain copies since there is a global “vulnerability market” that will pay hundreds of thousands to millions of dollars for copies of such ‘weapons’. Similarly, contractors and companies who obtain such ‘weapons’ sometimes use them for their own purposes, obtaining advantage over their competitors in selling ‘hacking’ services…
In addition to its operations in Langley, Virginia the CIA also uses the U.S. consulate in Frankfurt as a covert base for its hackers covering Europe, the Middle East and Africa….
If there is a military analogy to be made, the infestation of a target is perhaps akin to the execution of a whole series of military maneuvers against the target’s territory including observation, infiltration, occupation and exploitation...
The CIA’s hand crafted hacking techniques pose a problem for the agency. Each technique it has created forms a “fingerprint” that can be used by forensic investigators to attribute multiple different attacks to the same entity…The CIA’s Remote Devices Branch’s UMBRAGE group collects and maintains a substantial library of attack techniques ‘stolen’ from malware produced in other states including the Russian Federation. With UMBRAGE and related projects the CIA cannot only increase its total number of attack types but also misdirect attribution by leaving behind the “fingerprints” of the groups that the attack techniques were stolen from.
Excerpts from, Vault 7: CIA Hacking Tools Revealed, Wikileaks Press Release, Mar. 7, 2017



 On June 22nd 2017,
On June 22nd 2017, 

 On 7 March 2017, WikiLeaks began its new series of leaks on the U.S. Central Intelligence Agency…code-named “Vault 7” by WikiLeaks..
On 7 March 2017, WikiLeaks began its new series of leaks on the U.S. Central Intelligence Agency…code-named “Vault 7” by WikiLeaks..