The strike on IDT, a conglomerate,… was similar to WannaCry in one way: Hackers locked up IDT data and demanded a ransom to unlock it. But the ransom demand was just a smoke screen for a far more invasive attack that stole employee credentials. With those credentials in hand, hackers could have run free through the company’s computer network, taking confidential information or destroying machines….Were it not for a digital black box that recorded everything on IDT’s network, …the attack might have gone unnoticed.
Scans for the two hacking tools used against IDT indicate that the company is not alone. In fact, tens of thousands of computer systems all over the world have been “backdoored” by the same N.S.A. weapons. Mr. Ben-Oni and other security researchers worry that many of those other infected computers are connected to transportation networks, hospitals, water treatment plants and other utilities…
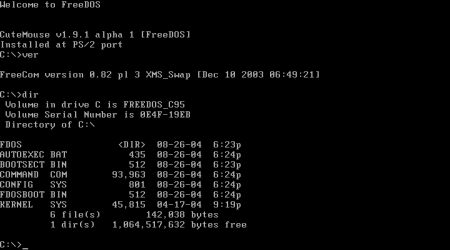
Both WannaCry and the IDT attack used a hacking tool the agency had code-named EternalBlue. The tool took advantage of unpatched Microsoft servers to automatically spread malware from one server to another, so that within 24 hours… hackers had spread their ransomware to more than 200,000 servers around the globe. The attack on IDT went a step further with another stolen N.S.A. cyberweapon, called DoublePulsar. The N.S.A. used DoublePulsar to penetrate computer systems without tripping security alarms. It allowed N.S.A. spies to inject their tools into the nerve center of a target’s computer system, called the kernel, which manages communications between a computer’s hardware and its software.
In the pecking order of a computer system, the kernel is at the very top, allowing anyone with secret access to it to take full control of a machine. It is also a dangerous blind spot for most security software, allowing attackers to do what they want and go unnoticed. In IDT’s case, attackers used DoublePulsar to steal an IDT contractor’s credentials. Then they deployed ransomware in what appears to be a cover for their real motive: broader access to IDT’s businesses…
But the attack struck Mr. Ben-Oni as unique. For one thing, it was timed perfectly to the Sabbath. Attackers entered IDT’s network at 6 p.m. on Saturday on the dot, two and a half hours before the Sabbath would end and when most of IDT’s employees — 40 percent of whom identify as Orthodox Jews — would be off the clock. For another, the attackers compromised the contractor’s computer through her home modem — strange.
The black box of sorts, a network recording device made by the Israeli security company Secdo, shows that the ransomware was installed after the attackers had made off with the contractor’s credentials. And they managed to bypass every major security detection mechanism along the way. Finally, before they left, they encrypted her computer with ransomware, demanding $130 to unlock it, to cover up the more invasive attack on her computer.
A month earlier, Microsoft had issued a software patch to defend against the N.S.A. hacking tools — suggesting that the agency tipped the company off to what was coming. Microsoft regularly credits those who point out vulnerabilities in its products, but in this case the company made no mention of the tipster. Later, when the WannaCry attack hit hundreds of thousands of Microsoft customers, Microsoft’s president, Brad Smith, slammed the government in a blog post for hoarding and stockpiling security vulnerabilities. For his part, Mr. Ben-Oni said he had rolled out Microsoft’s patches as soon as they became available, but attackers still managed to get in through the IDT contractor’s home modem.
There are now YouTube videos showing criminals how to attack systems using the very same N.S.A. tools used against IDT, and Metasploit, an automated hacking tool, now allows anyone to carry out these attacks with the click of a button….
“Once DoublePulsar is on the machine, there’s nothing stopping anyone else from coming along and using the back door,” Mr. Dillon said.More distressing, Mr. Dillon tested all the major antivirus products against the DoublePulsar infection and a demoralizing 99 percent failed to detect it. “We’ve seen the same computers infected with DoublePulsar for two months and there is no telling how much malware is on those systems,” Mr. Dillon said. “Right now we have no idea what’s gotten into these organizations.”..
Could that attack be coming? The Shadow Brokers resurfaced last month, promising a fresh load of N.S.A. attack tools, even offering to supply them for monthly paying subscribers — like a wine-of-the-month club for cyberweapon enthusiasts.
Excerpts from NICOLE PERLROTHJUNE, A Cyberattack ‘the World Isn’t Ready For’, New York Times, June 20, 2017