In the battle against illegal immigration, the U.S. is spending hundreds of millions of dollars on tools that give federal agents easy access to the home and workplace addresses of American citizens, their social-media accounts, vehicle information, flight history, law-enforcement records and other personal information, as well as data to track their daily comings and goings, The Wall Street Journal found. The government’s tracking system relies on an amalgam of public and private information sifted, sorted and packaged by contractors that include Palantir Technologies, Deloitte, Japanese conglomerate NEC and smaller spyware specialists.
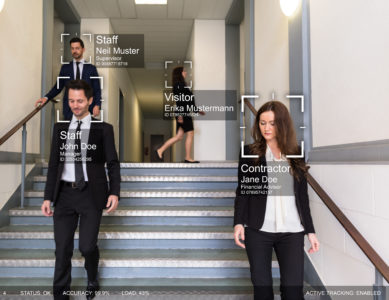
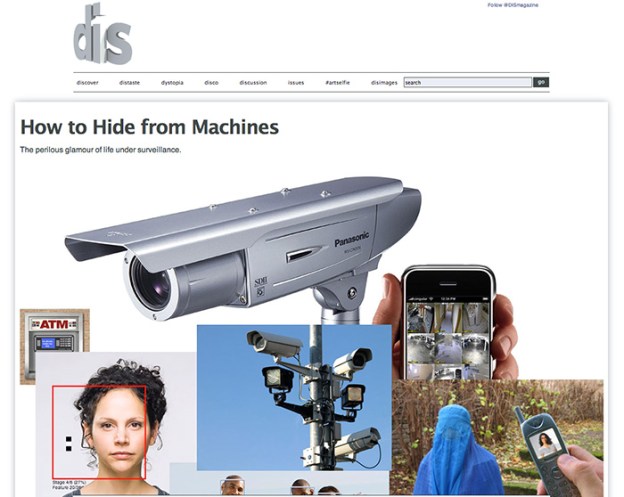
The Department of Homeland Security has put these surveillance tools—facial-recognition software, location tracking and social-media scrapers once aimed largely at suspected terrorists and drug-traffickers—in the hands of federal immigration agents, who can identify, research and track virtually anyone by entering a name, license plate or by simply taking a person’s photo.
The government surveillance system has advanced since the 9/11 terrorist attacks with the aid of artificial intelligence and the linking of government records with far-reaching commercial databases. It has been used against people whom the government alleged opposed or obstructed the immigration crackdown.
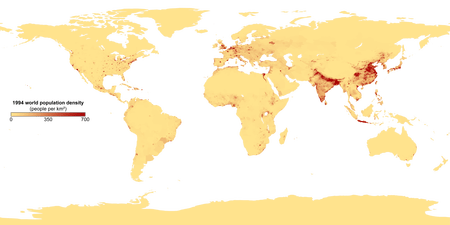
With the backing of Congress and President Trump, DHS spent a record $425 million on surveillance tech in 2025, a 17% increase from the prior year…Palantir is the top beneficiary of DHS’s stepped-up spending on deportation and surveillance work,… In 2025, DHS paid Palantir $30 million to put a broad span of information about individuals into an app on agents’ smartphones, allowing them to plot the location of people in the U.S. The app, known as Enhanced Leads Identification and Targeting for Enforcement, or ELITE, lets officers research and track individuals based on criminal history, license plate searches, name, date of birth or locations.
The results display on a map or as a list… The app pulls from a variety of government databases, including information compiled by private investigators known as “skip tracers” who track the current addresses of individuals. ..An ICE agent during court testimony last year compared ELITE to Google Maps: Targets appear as pins on a map, clustered around addresses where immigrants, including “lawful permanent residents,” are likely to live…
Through the year beginning in January 2025, the U.S. paid consulting firms, including Deloitte, $130 million, to aid ICE’s deportation efforts and law enforcement support work. New consultant contracts call for analysts to monitor people on social media, identify threats and create dossiers about people who make them. DHS awarded $15 million to tech company Cellebrite for forensic tools to unlock phones and extract call logs, GPS location data, text messages, deleted photos, contacts and email addresses. US. Customs and Border Protection (CBP) renewed agreements with vehicle-forensics firm Berla to retrieve data, including travel history, from the vehicles of suspects. In 2025, DHS reactivated a $2 million contract with the U.S. subsidiary of Israeli spyware company Paragon Solutions, which makes Graphite, a hacking tool that can infiltrate encrypted messaging apps such as Signal and WhatsApp.
Since January 2025, DHS has announced plans to spend up to nearly $200 million on new surveillance contracts. of which $100 million for Babel Street Insight which provides an AI-driven platform to translate social-media posts from hundreds of languages, map networks of contacts and scan for what the company calls “expressions of violent intent” and “negative” sentiments. Nearly $21 million went to companies that track and identify targets with biometric technology. That included $8 million to NEC for a facial-recognition algorithm that identifies passengers boarding planes. DHS rolled out an app last year that allows agents to identify people from images, using NEC technology. DHS also expanded its use of Clearview AI, another facial-recognition database, which contains more than 70 billion photos.
Excerpt from Shane Shifflett, ‘We Know You Live Right Here’: No Secrets in America’s New Surveillance Dragnet, WSJ, Apr. 30, 2026