Sam Altman wants to save us from the AI-dominated world he is building. The trouble is, governments aren’t buying his plan, which involves an attempt to scan the eyeballs of every person on Earth and pay them with his own cryptocurrency-the Worldcoin. But Worldcoin has come under assault by authorities over its mission. It has been raided in Hong Kong, blocked in Spain, fined in Argentina and criminally investigated in Kenya. A ruling looms on whether it can keep operating in the European Union….Among the concerns: How does the Cayman Islands-registered Worldcoin Foundation handle user data, train its algorithms and avoid scanning children?
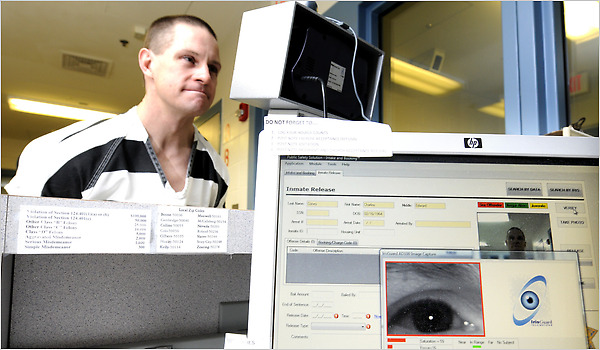
Worldcoin verifies “humanness” by scanning irises using a basketball-sized chrome device called the Orb. Worldcoin says irises, which are complex and relatively unchanging in adults, can better distinguish humans than fingerprints or faces. Users receive immutable codes held in an online “World ID” passport, to use on other platforms to prove they are human, plus payouts in Worldcoin’s WLD cryptocurrency. Worldcoin launched in 2023 and says it has verified more than six million people across almost 40 countries. Based on recent trading prices, the total pool of WLD is theoretically worth some $15 billion.
Altman says his technology is completely private: Orbs delete all images after verification, and iris codes contain no personal information—unless users permit Worldcoin to train its algorithms with their scans. Encrypted servers hold the anonymized codes and images. However, several authorities have accused Worldcoin of telling Orb operators, typically independent contractors, to encourage users to hand over iris images. Privacy advocates say these could be used to build a global biometric database with little oversight.
Excerpt from Angus Berwick, Sam Altman’s Worldcoin Is Battling With Governments Over Your Eyes, WSJ, Aug. 18, 2024