Vladimir Putin, Russia’s president, has portrayed his aggression on the Ukrainian border as pushing back against Western advances. For some time he has been doing much the same online. He has long referred to the internet as a “CIA project”. His deep belief that the enemy within and the enemy without are in effect one and the same… Faced with such “aggression”, Mr Putin wants a Russian internet that is secure against external threat and internal opposition. He is trying to bring that about on a variety of fronts: through companies, the courts and technology itself.
In December 2021, VK, one of Russia’s online conglomerates, was taken over by two subsidiaries of Gazprom, the state-owned gas giant. In the same month a court in Moscow fined Alphabet, which owns Google, a record $98m for its repeated failure to delete content the state deems illegal. And Mr Putin’s regime began using hardware it has required internet service providers (ISPS) to install to block Tor, a tool widely used in Russia to mask online activity. All three actions were part of the country’s effort to assure itself of online independence by building what some scholars of geopolitics, borrowing from Silicon Valley, have begun calling a “stack”.
In technology, the stack is the sum of all the technologies and services on which a particular application relies, from silicon to operating system to network. In politics it means much the same, at the level of the state. The national stack is a sovereign digital space made up not only of software and hardware (increasingly in the form of computing clouds) but also infrastructure for payments, establishing online identities and controlling the flow of information…
China built its sovereign digital space with censorship in mind. The Great Firewall, a deep-rooted collection of sophisticated digital checkpoints, allows traffic to be filtered with comparative ease. The size of the Chinese market means that indigenous companies, which are open to various forms of control, can successfully fulfil all of their users’ needs. And the state has the resources for a lot of both censorship and surveillance. Mr Putin and other autocrats covet such power. But they cannot get it. It is not just that they lack China’s combination of rigid state control, economic size, technological savoir-faire and stability of regime. They also failed to start 25 years ago. So they need ways to achieve what goals they can piecemeal, by retrofitting new controls, incentives and structures to an internet that has matured unsupervised and open to its Western begetters.
Russia’s efforts, which began as purely reactive attempts to lessen perceived harm, are becoming more systematic. Three stand out: (1) creating domestic technology, (2) controlling the information that flows across it and, perhaps most important, (3) building the foundational services that underpin the entire edifice.
Russian Technology
The government has made moves to restart a chipmaking plant in Zelenograd near Moscow, the site of a failed Soviet attempt to create a Silicon Valley. But it will not operate at the cutting edge. So although an increasing number of chips are being designed in Russia, they are almost all made by Samsung and TSMC, a South Korean and a Taiwanese contract manufacturer. This could make the designs vulnerable to sanctions….
For crucial applications such as mobile-phone networks Russia remains highly reliant on Western suppliers, such as Cisco, Ericsson and Nokia. Because this is seen as leaving Russia open to attacks from abroad, the industry ministry, supported by Rostec, a state-owned arms-and-technology giant, is pushing for next-generation 5g networks to be built with Russian-made equipment only. The country’s telecoms industry does not seem up to the task. And there are internecine impediments. Russia’s security elites, the siloviki, do not want to give up the wavelength bands best suited for 5g. But the only firm that could deliver cheap gear that works on alternative frequencies is Huawei, an allegedly state-linked Chinese electronics group which the siloviki distrust just as much as security hawks in the West do.
It is at the hardware level that Russia’s stack is most vulnerable. Sanctions imposed may treat the country, as a whole, like Huawei is now treated by America’s government. Any chipmaker around the world that uses technology developed in America to design or make chips for Huawei needs an export license from the Commerce Department in Washington—which is usually not forthcoming. If the same rules are applied to Russian firms, anyone selling to them without a license could themselves risk becoming the target of sanctions. That would see the flow of chips into Russia slow to a trickle.
When it comes to software the Russian state is using its procurement power to amp up demand. Government institutions, from schools to ministries, have been encouraged to dump their American software, including Microsoft’s Office package and Oracle’s databases. It is also encouraging the creation of alternatives to foreign services for consumers, including TikTok, Wikipedia and YouTube. Here the push for indigenization has a sturdier base on which to build. Yandex, a Russian firm which splits the country’s search market with Alphabet’s Google, and VK, a social-media giant, together earned $1.8bn from advertising last year, more than half of the overall market. VK’s vKontakte and Odnoklassniki trade places with American apps (Facebook, Instagram) and Chinese ones (Likee, TikTok) on the top-ten downloads list.
This diverse system is obviously less vulnerable to sanctions—which are nothing like as appealing a source of leverage here as they are elsewhere in the stack. Making Alphabet and Meta stop offering YouTube and WhatsApp, respectively, in Russia would make it much harder for America to launch its own sorties into Russian cyberspace. So would disabling Russia’s internet at the deeper level of protocols and connectivity. All this may push Russians to use domestic offerings more, which would suit Mr Putin well.
As in China, Russia is seeing the rise of “super-apps”, bundles of digital services where being local makes sense. Yandex is not just a search engine. It offers ride-hailing, food delivery, music-streaming, a digital assistant, cloud computing and, someday, self-driving cars. Sber, Russia’s biggest lender, is eyeing a similar “ecosystem” of services, trying to turn the bank into a tech conglomerate. In the first half of 2021 alone it invested $1bn in the effort, on the order of what biggish European banks spend on information technology (IT). Structural changes in the IT industry are making some of this Russification easier. Take the cloud. Its data centres use cheap servers made of off-the-shelf parts and other easily procured commodity kit. Much of its software is open-source. Six of the ten biggest cloud-service providers in Russia are now Russian…The most successful ones are “moving away from proprietary technology” sold by Western firms (with the exception of chips)…
Information Flow
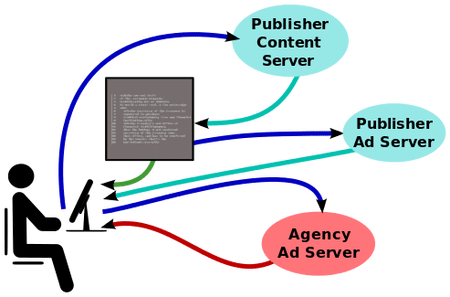
If technology is the first part of Russia’s stack, the “sovereign internet” is the second. It is code for how a state controls the flow of information online. In 2019 the government amended several laws to gain more control of the domestic data flow. In particular, these require ISPS to install “technical equipment for counteracting threats to stability, security and functional integrity”. This allows Roskomnadzor, Russia’s internet watchdog, to have “middle boxes” slipped into the gap between the public internet and an ISPS’ customers. Using “deep packet inspection” (DPI), a technology used at some Western ISPS to clamp down on pornography, these devices are able to throttle or block traffic from specific sources (and have been deployed in the campaign against Tor). DPI kit sits in rooms with restricted access within the ISPS’ facilities and is controlled directly from a command center at Roskomnadzor. This is a cheap but imperfect version of China’s Great Firewall.
Complementing the firewall are rules that make life tougher for firms. In the past five years Google has fielded 20,000-30,000 content-removal requests annually from the government in Russia, more than in any other country. From this year 13 leading firms—including Apple, TikTok and Twitter—must employ at least some content moderators inside Russia. This gives the authorities bodies to bully should firms prove recalcitrant. The ultimate goal may be to push foreign social media out of Russia altogether, creating a web of local content… But this Chinese level of control would be technically tricky. And it would make life more difficult for Russian influence operations, such as those of the Internet Research Agency, to use Western sites to spread propaganda, both domestically and abroad.
Infrastructure
Russia’s homegrown stack would still be incomplete without a third tier: the services that form the operating system of a digital state and thus provide its power. In its provision of both e-government and payment systems, Russia puts some Western countries to shame. Gosuslugi (“state services”) is one of the most-visited websites and most-downloaded apps in Russia. It hosts a shockingly comprehensive list of offerings, from passport application to weapons registration. Even critics of the Kremlin are impressed, not least because Russia’s offline bureaucracy is hopelessly inefficient and corrupt. The desire for control also motivated Russia’s leap in payment systems. In the wake of its annexation of Crimea, sanctions required MasterCard and Visa, which used to process most payments in Russia, to ban several banks close to the regime. In response, Mr Putin decreed the creation of a “National Payment Card System”, which was subsequently made mandatory for many transactions. Today it is considered one of the world’s most advanced such schemes. Russian banks use it to exchange funds. The “Mir” card which piggybacks on it has a market share of more than 25%, says GlobalData, an analytics firm.
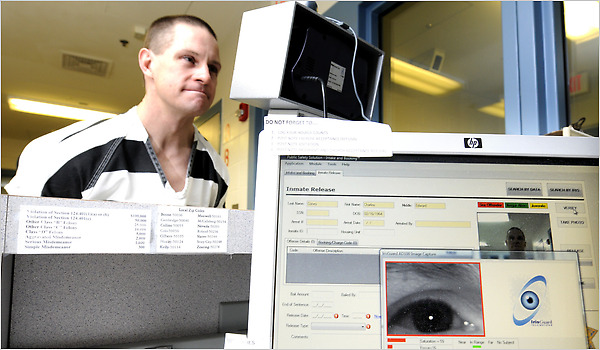
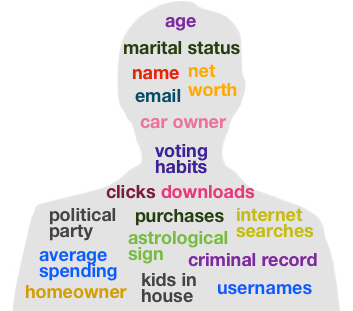
Other moves are less visible. A national version of the internet’s domain name system, currently under construction, allows Russia’s network to function if cut off from the rest of the world (and gives the authorities a new way to render some sites inaccessible). Some are still at early stages. A biometric identity system, much like India’s Aadhaar, aims to make it easier for the state to keep track of citizens and collect data about them while offering new services. (Muscovites can now pay to take the city’s metro just by showing their face.) A national data platform would collect all sorts of information, from tax to health records—and could boost Russia’s efforts to catch up in artificial intelligence (AI).
Excerpt from Digital geopolitics: Russia is trying to build its own great firewall, Economist, Feb. 19, 2022





 The
The