The current standard method for validating a user’s identity for authentication on an information system requires humans to do something that is inherently difficult: create, remember, and manage long, complex passwords. Moreover, as long as the session remains active, typical systems incorporate no mechanisms to verify that the user originally authenticated is the user still in control of the keyboard. Thus, unauthorized individuals may improperly obtain extended access to information system resources if a password is compromised or if a user does not exercise adequate vigilance after initially authenticating at the console.
The Active Authentication program seeks to address this problem by developing novel ways of validating the identity of the person at the console that focus on the unique aspects of the individual through the use of software-based biometrics. Biometrics is defined as the characteristics used to uniquely recognize humans based upon one or more intrinsic physical or behavioral traits. This program focuses on the computational behavioral traits that can be observed through how we interact with the world. Just as when you touch something with our finger you leave behind a fingerprint, when you interact with technology you do so in a pattern based on how your mind processes information, leaving behind a “cognitive fingerprint.”
This BAA addresses the first phase of this program. In the first phase of the program, the focus will be on researching biometrics that does not require the installation of additional hardware sensors. Rather, DARPA will look for research on biometrics that can be captured through the technology already in use in a standard DoD office environment, looking for aspects of the “cognitive fingerprint.” A heavy emphasis will be placed on validating any potential new biometrics with empirical tests to ensure they would be effective in large scale deployments.
The later planned phases of the program that are not addressed in this BAA will focus on developing a solution that integrates any available biometrics using a new authentication platform suitable for deployment on a standard Department of Defense desktop or laptop. The planned combinatorial approach of using multiple modalities for continuous user identification and authentication is expected to deliver a system that is accurate, robust, and transparent to the user’s normal computing experience. The authentication platform is planned to be developed with open Application Programming Interfaces (APIs) to allow the integration of other software or hardware biometrics available in the future from any source.
The combined aspects of the individual that this program is attempting to uncover are the aspects that are the computational behavioral “fingerprint” of the person at the keyboard. This has also been referred to in existing research as the “cognitive fingerprint.” The proposed theory is that how individuals formulate their thoughts and actions are reflected through their behavior, and this behavior in turn can be captured as metrics in how the individual performs tasks using the computer.
Some examples of the computational behavior metrics of the cognitive fingerprint include:
− keystrokes
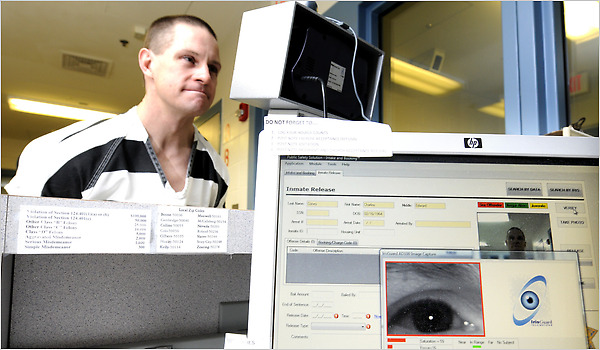
− eye scans
− how the user searches for information (verbs and predicates used)
− how the user selects information (verbs and predicates used)
− how the user reads the material selected
• eye tracking on the page
• speed with which the individual reads the content
− methods and structure of communication (exchange of email)
These examples are only provided for illustrative purposes and are not intended as a list of potential research topics. The examples above include potential biometrics that would not be supported through this BAA due to a requirement for the deployment of additional hardware based sensors (such as tracking eye scans).
Excerpt from, Broad Agency Announcement, Active Authentication, DARPA-BAA-12-06, January 12, 2012
On Feb. 12, 2013, two groups announced related projects. The first is an industry group calling itself the FIDO (Fast IDentity Online) Alliance. It consists of the computer-maker, Lenovo, the security firm, Nok Nok Labs, the online payment giant, PayPal, the biometrics experts, Agnito, and the authentication specialists, Validity. The second is the Defense Advanced Research Project Agency (DARPA), a research and development arm of the Defense Department.
Excerpt from DARPA, FIDO Alliance Join Race to Replace Passwords, CNET, Feb. 12, 2013