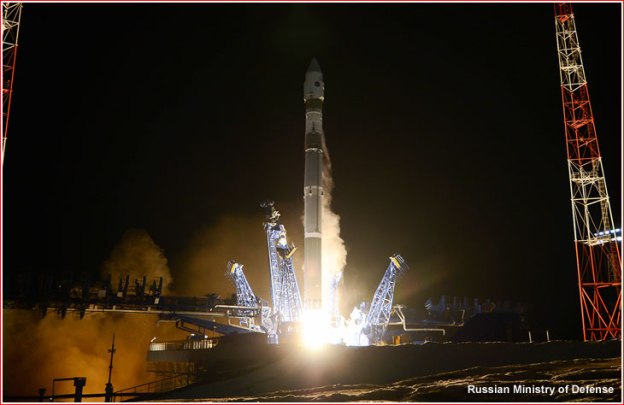
In March 2018, India became only the fourth country in the world—after Russia, the US, and China—to successfully destroy a satellite in orbit. Mission Shakti, as it was called, was a demonstration of a direct-ascent anti-satellite weapon (ASAT)—or in plain English, a missile launched from the ground. Typically this type of ASAT has a “kill vehicle,” essentially a chunk of metal with its own guidance system, mounted on top of a ballistic missile. Shortly after the missile leaves the atmosphere, the kill vehicle detaches from it and makes small course corrections as it approaches the target. No explosives are needed; at orbital speeds, kinetic energy does the damage…. China’s own first successful ASAT test was in 2007….
But going to war in space… doesn’t necessarily mean blowing up satellites. Less aggressive methods typically involve cyberattacks to interfere with the data flows between satellites and the ground stations. Satellites are, after all, computers that happen to be in space, so they are vulnerable to attacks that disable or hijack them, just like their terrestrial peers.
For example, in 2008, a cyberattack on a ground station in Norway let someone cause 12 minutes of interference with NASA’s Landsat satellites. Later that year, hackers gained access to NASA’s Terra Earth observation satellite and did everything but issue commands. It’s not clear if they could have done so but chose not to. Nor is it clear who was behind the attack, although some commentators at the time pointed the finger at China. Experts warn that hackers could shut off a satellite’s communications, rendering it useless. Or they could permanently damage it by burning off all its propellant or pointing its imaging sensor at the sun to burn it out.
Another common mode of attack is to jam or spoof satellite signals. There is nothing fancy about this: it’s easier than hacking, and all the gear required is commercially available. Jammers, often mounted on the back of trucks, operate at the same frequency as GPS or other satellite communication systems to block their signals. …There are strong suspicions that Russia has been jamming GPS signals during NATO exercises in Norway and Finland, and using similar tactics in other conflicts. “Russia is absolutely attacking space systems using jammers throughout the Ukraine,” says Weeden. Jamming is hard to distinguish from unintentional interference, making attribution difficult (the US military regularly jams its own communications satellites by accident). A recent report from the US Defense Intelligence Agency (DIA) claims that China is now developing jammers that can target a wide range of frequencies, including military communication bands. North Korea is believed to have bought jammers from Russia, and insurgent groups in Iraq and Afghanistan have been known to use them too.
Spoofing, meanwhile, puts out a fake signal that tricks GPS or other satellite receivers on the ground…. Russia also seems to use spoofing as a way of protecting critical infrastructure,,,.As well as being hard to pin on anyone, jamming and spoofing can sow doubt in an enemy’s mind about whether they can trust their own equipment when needed. The processes can also be switched off at any time, which makes attribution even harder.
The 2019 Defense Intelligence Agency (DIA) report suggests that China will have a ground-based laser that can destroy a satellite’s optical sensors in low Earth orbit as early as next year (and that will, by the mid-2020s, be capable of damaging the structure of the satellite). Generally, the intention with lasers is not to blast a satellite out of the sky but to overwhelm its image sensor so it can’t photograph sensitive locations. The damage can be temporary, unless the laser is powerful enough to make it permanent…In 2006, US officials claimed that China was aiming lasers at US imaging satellites passing over Chinese territory.
“It’s happening all the time at this low level,” says Harrison. “It’s more gray-zone aggression. Countries are pushing the limits of accepted behavior and challenging norms. They’re staying below the threshold of conflict.”..
The suspicion is that China is practicing for something known as a co-orbital attack, in which an object is sent into orbit near a target satellite, maneuvers itself into position, and then waits for an order. Such exercises could have less aggressive purposes—inspecting other satellites or repairing or disposing of them, perhaps. But co-orbiting might also be used to jam or snoop on enemy satellites’ data, or even to attack them physically….Russia, too, has been playing about in geostationary orbit. One of its satellites, Olymp-K, began moving about regularly, at one point getting in between two Intelsat commercial satellites. Another time, it got so close to a French-Italian military satellite that the French government called it an act of “espionage.” The US, similarly, has tested a number of small satellites that can maneuver around in space.
As the dominant player in space for decades, the US now has the most to lose. The DIA report points out that both China and Russia reorganized their militaries to give space warfare a far more central role. In response, the US military is starting to make satellites tougher to find and attack. For instance, the NTS-3, a new experimental GPS satellite scheduled for launch in 2022, will have programmable, steerable antennas that can broadcast at higher power to counter jamming. It’s designed to remain accurate even if it loses its connection with ground controllers, and to detect efforts to jam its signal.
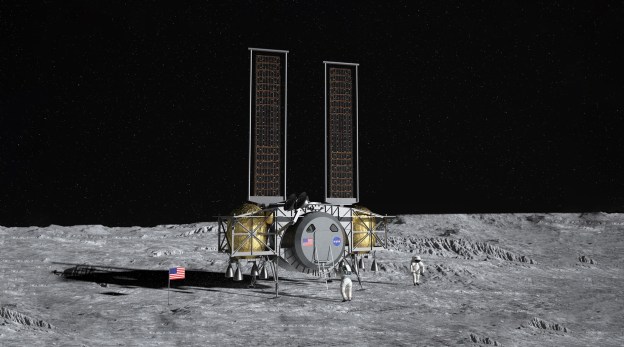
Another solution is not just to make single satellites more resilient, but to use constellations in which any one satellite is not that important. That’s the thinking behind Blackjack, a new DARPA program to create a cheap network of military communications satellites in low Earth orbit.
Excerpts from Niall Firth How to fight a war in space (and get away with it), MIT Technology Review, June 26, 2019